On April 8, 2026, Anthropic announced Project Glasswing, a cybersecurity initiative powered by Claude Mythos Preview, its newest and most powerful frontier model. The announcement confirms what a March data leak first revealed: Mythos is, by a wide margin, the most capable AI model Anthropic has ever built.
Mythos Preview can find software vulnerabilities better than all but the most skilled humans. It has already discovered thousands of high-severity zero-day vulnerabilities, including flaws in every major operating system and every major web browser. Some of these bugs had gone undetected for over two decades.
Anthropic is not making Mythos Preview generally available. Instead, the company has partnered with AWS, Apple, Google, Microsoft, NVIDIA, CrowdStrike, and others to deploy the model defensively, giving cyber defenders a head start before models this capable become widespread.
Introducing Project Glasswing: an urgent initiative to help secure the world’s most critical software.
— Anthropic (@AnthropicAI) April 7, 2026
It’s powered by our newest frontier model, Claude Mythos Preview, which can find software vulnerabilities better than all but the most skilled humans.https://t.co/NQ7IfEtYk7
What Is Claude Mythos
Claude Mythos is a new AI model from Anthropic that sits above the company’s existing Opus tier. The leaked draft blog post from March 2026 described it plainly: “larger and more intelligent than our Opus models, which were, until now, our most powerful.”
Until Mythos, Anthropic’s model hierarchy was Haiku (fast, cheap), Sonnet (balanced), and Opus (most capable). Mythos introduces an entirely new tier above Opus, representing a significant jump in capability rather than an incremental update.
Anthropic chose the name Mythos “to evoke the deep connective tissue that links together knowledge and ideas.” The model has completed training and is now being deployed through Project Glasswing as “Claude Mythos Preview,” a limited-access version focused on cybersecurity applications.
Mythos vs Capybara
You may have seen both “Mythos” and “Capybara” used in connection with this model. The leaked blog post on Anthropic’s CMS actually contained two versions of the same draft, one using “Mythos” throughout and one with “Capybara” replacing many instances of the name.
There are two prevailing theories about the naming:
Capybara as a codename. The original version of the draft used only “Mythos.” Shortly after, an updated version appeared with “Capybara” swapped in. This suggests Capybara may be an internal codename used during development, with Mythos being the intended public name.
Capybara as a tier name. Some reporting interprets Capybara as the name for the new model tier (similar to how Haiku, Sonnet, and Opus are tiers), with Mythos being the specific model within that tier. The leaked draft does refer to Capybara as “a new name for a new tier of model.”
Either way, both names refer to the same underlying model. The press and public have largely settled on “Claude Mythos” as the go-to name, and Anthropic’s official announcement uses “Claude Mythos Preview.”
Project Glasswing
Project Glasswing is a collaborative cybersecurity initiative announced on April 8, 2026. It brings together 12 major organizations to use Claude Mythos Preview for defensive security work, scanning and fixing vulnerabilities in the world’s most critical software.
The founding partners include Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, the Linux Foundation, Microsoft, NVIDIA, and Palo Alto Networks.
AI models have reached a level of coding capability where they can find and exploit software vulnerabilities better than nearly all humans. Rather than waiting for these capabilities to proliferate, Anthropic wants to deploy them defensively first. As the company put it: “The window between a vulnerability being discovered and being exploited by an adversary has collapsed. What once took months now happens in minutes with AI.”
Anthropic has committed up to $100M in Mythos Preview usage credits for its partners and over 40 additional organizations that maintain critical software, including open-source projects. The company is also donating $2.5M to Alpha-Omega and OpenSSF (via the Linux Foundation) and $1.5M directly to the Apache Software Foundation.
Within 90 days, Anthropic will report publicly on what it has learned, including vulnerabilities fixed and recommendations for disclosure, patching, and development practices.
Benchmarks and Capabilities
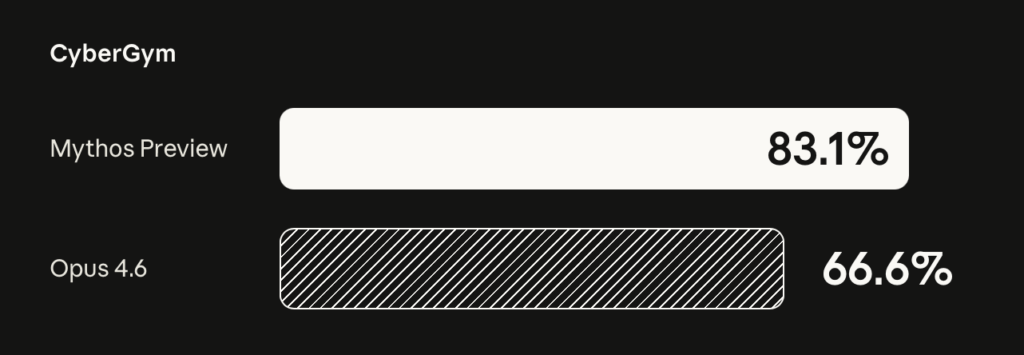
With the official announcement, Anthropic released concrete benchmark numbers that confirm the leaked draft’s claims. Mythos Preview outperforms Claude Opus 4.6 significantly across coding, reasoning, and cybersecurity tasks.
Coding benchmarks:
| Benchmark | Claude Opus 4.6 | Claude Mythos Preview |
|---|---|---|
| SWE-bench Verified | 80.8% | 93.9% |
| SWE-bench Pro | 53.4% | 77.8% |
| SWE-bench Multilingual | 77.8% | 87.3% |
| SWE-bench Multimodal | 27.1% | 59.0% |
| Terminal-Bench 2.0 | 65.4% | 82.0% |
Reasoning benchmarks:
| Benchmark | Claude Opus 4.6 | Claude Mythos Preview |
|---|---|---|
| GPQA Diamond | 91.3% | 94.6% |
| Humanity’s Last Exam (with tools) | 53.1% | 64.7% |
| BrowseComp | 83.7% | 86.9% |
| OSWorld-Verified | 72.7% | 79.6% |
Cybersecurity:
| Benchmark | Claude Opus 4.6 | Claude Mythos Preview |
|---|---|---|
| CyberGym Vulnerability Reproduction | 66.6% | 83.1% |
The 93.9% on SWE-bench Verified and 77.8% on SWE-bench Pro put Mythos Preview well ahead of any publicly available model. The jump from 27.1% to 59.0% on SWE-bench Multimodal is particularly notable, more than doubling Opus 4.6’s score on visual and multi-modal coding tasks.
Anthropic describes these capabilities as emergent. The exploit development abilities were not explicitly trained but arose as a downstream consequence of general improvements in code reasoning and autonomy.
How Mythos Compares to Claude Opus 4.6
| Aspect | Claude Opus 4.6 | Claude Mythos Preview |
|---|---|---|
| Model tier | Opus | New tier (above Opus) |
| Model size | Large | Larger than Opus |
| SWE-bench Verified | 80.8% | 93.9% |
| SWE-bench Pro | 53.4% | 77.8% |
| Terminal-Bench 2.0 | 65.4% | 82.0% |
| GPQA Diamond | 91.3% | 94.6% |
| Cybersecurity | 66.6% CyberGym | 83.1% CyberGym |
| Context window | Up to 1M tokens | Unknown |
| Pricing | $5/$25 per million tokens | $25/$125 per million tokens |
| Availability | Generally available | Limited access via Project Glasswing |
At $25 per million input tokens and $125 per million output tokens, Mythos costs 5x more than Opus 4.6. Those prices apply after the initial research phase, during which partners receive credits.
The model will be available through the Claude API, Amazon Bedrock, Google Cloud’s Vertex AI, and Microsoft Foundry.
Vulnerabilities Discovered by Mythos
Anthropic’s technical report details the specific vulnerabilities Mythos Preview found during approximately one month of testing. The model identified thousands of zero-day vulnerabilities across major software, many of them decades old.
OpenBSD (27 years old). A signed integer overflow in OpenBSD’s TCP SACK implementation that allows remote denial-of-service, crashing any OpenBSD host via a specially crafted TCP connection. OpenBSD is widely considered one of the most security-hardened operating systems in existence, and this bug survived 27 years of manual auditing.
FFmpeg (16 years old). An out-of-bounds heap write in the H.264 codec that automated testing tools had hit five million times without ever flagging. The bug involves a slice counter collision with a sentinel value (65535) causing an array index mismatch. Mythos found it autonomously at a cost of approximately $10,000 across several hundred repository scans.
FreeBSD NFS (17 years old). A stack buffer overflow in RPCSEC_GSS authentication (CVE-2026-4747) enabling complete unauthenticated root access from the network. Mythos autonomously developed a 20-gadget ROP chain split across six sequential RPC packets to exploit it. Opus 4.6, by comparison, required human guidance to exploit the same vulnerability.
Linux kernel privilege escalation. Mythos chained multiple vulnerabilities together (KASLR bypasses, use-after-free bugs, heap sprays) to achieve full root privilege escalation. The model found nearly a dozen different working combinations, each exploiting a different set of kernel bugs. In one case, it converted a single-bit out-of-bounds write from a 16-year-old ipset bug into full root access in under half a day for less than $1,000.
Web browser exploits. Zero-day vulnerabilities in every major browser, including JIT heap sprays with sandbox escapes. Some were escalated to cross-origin bypasses and OS kernel writes from JavaScript context. All were unpatched at publication. For comparison, Opus 4.6 produced 2 successful Firefox exploits from several hundred attempts. Mythos Preview produced 181 working exploits with 29 additional register-control cases.
Cryptography libraries. Weaknesses in TLS, AES-GCM, and SSH implementations that could enable certificate forgery and decryption of encrypted communications. Two of three identified vulnerabilities were unpatched at the time of writing.
Virtual machine monitor. A guest-to-host memory corruption vulnerability in a memory-safe language (Rust/Java unsafe operations) enabling out-of-bounds writes to host process memory. Details are being withheld pending disclosure.
Human reviewers examined 198 vulnerability reports and agreed with the model’s severity assessment 89% of the time (exact match), rising to 98% within one severity level. The projected total includes over 1,000 critical-severity and thousands of high-severity findings.
Anthropic also notes that engineers without formal security training were able to use Mythos to obtain working exploits. The model’s capabilities are not limited to expert users.
The Cybersecurity Factor
The cybersecurity angle is what rattled markets in March and drove the creation of Project Glasswing in April.
The leaked draft warned that Mythos “presages an upcoming wave of models that can exploit vulnerabilities in ways that far outpace the efforts of defenders.” The official announcement backs this up with concrete evidence: bugs that survived decades of expert auditing, millions of automated test runs, and exploitation chains that previously required elite human researchers, all produced autonomously by the model.
The same capabilities that make Mythos effective for offense make it valuable for defense. Project Glasswing is built on this premise: deploy the model defensively before similar capabilities become widespread.
Anthropic has also announced a “Cyber Verification Program” that will let legitimate security professionals apply for exceptions to the model’s built-in safeguards, enabling authorized defensive research while blocking malicious use.
Partners and Funding
Launch partners (12 organizations):
AWS, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, Linux Foundation, Microsoft, NVIDIA, Palo Alto Networks, and Anthropic.
Extended access:
Over 40 additional organizations that maintain critical software, including open-source projects.
Financial commitments:
– $100M in Mythos Preview usage credits for partners and critical software maintainers
– $2.5M to Alpha-Omega and OpenSSF via the Linux Foundation
– $1.5M to the Apache Software Foundation
The partner list notably includes companies that were hit by the initial stock sell-off. Both CrowdStrike and Palo Alto Networks saw significant drops when the Mythos leak first broke, and both are now founding partners in the defensive initiative.
How the Leak Happened
The irony of an AI safety company accidentally leaking its most sensitive model through a misconfigured database has not gone unnoticed.
Security researchers Roy Paz of LayerX Security and Alexandre Pauwels of the University of Cambridge discovered that close to 3,000 unpublished assets on Anthropic’s website were publicly accessible. These included images, PDFs, audio files, and draft blog posts describing Claude Mythos in detail.
The root cause was a configuration error in Anthropic’s content management system. Assets uploaded to the CMS were public by default unless someone explicitly changed a setting to keep them private. Anthropic forgot to restrict access to the Mythos materials.
After Fortune reviewed the documents and contacted Anthropic, the company restricted public access and acknowledged the leak as “human error.” As one Futurism article put it, Anthropic “leaked upcoming model with unprecedented cybersecurity risks in the most ironic way possible.”
Market Impact
The leak triggered an immediate sell-off in cybersecurity stocks on March 27, 2026. If AI can find and exploit vulnerabilities faster than humans can patch them, the value proposition of existing cybersecurity companies takes a hit.
| Company | Ticker | Drop |
|---|---|---|
| Tenable | TENB | 9% |
| Okta | OKTA | 7%+ |
| Netskope | Private | 7%+ |
| CrowdStrike | CRWD | 6-7% |
| Palo Alto Networks | PANW | 6-7% |
| SentinelOne | S | 6% |
| Zscaler | ZS | 4.5-6% |
| iShares Cybersecurity ETF | CIBR | 4.5% |
Broader software stocks and Bitcoin also slid. Analysts at Evercore noted the model’s capabilities raise questions about whether AI could fundamentally reshape the cybersecurity landscape. The Pentagon has also reportedly taken interest, seeing potential applications for national defense.
The Project Glasswing announcement on April 8 may help stabilize sentiment, given that several of the hardest-hit companies (CrowdStrike, Palo Alto Networks) are now official partners in the defensive initiative.
When Can You Use Claude Mythos
As of April 8, 2026, Claude Mythos Preview is not available to the general public.
- Project Glasswing partners have access for defensive security work through the Claude API, Amazon Bedrock, Google Cloud’s Vertex AI, and Microsoft Foundry.
- 40+ additional organizations that maintain critical software are receiving extended access.
- No general availability planned for Mythos Preview specifically. Anthropic has stated it “does not plan to make Claude Mythos Preview generally available.”
- Pricing for post-research usage is $25/$125 per million input/output tokens (5x the cost of Opus 4.6).
- Safeguards first. Anthropic will “launch new safeguards with an upcoming Claude Opus model” before deploying Mythos-class capabilities more broadly.
- Cyber Verification Program will let legitimate security professionals apply for exceptions to built-in safeguards.
Anthropic is not ruling out Mythos-class capabilities for general use forever. The goal is to “deploy Mythos-class models safely at scale,” but the company needs safeguards that reliably block the most dangerous outputs first. Those safeguards will be tested with an upcoming Claude Opus model before any broader rollout.
What This Means for You
For developers and engineers. A model scoring 93.9% on SWE-bench Verified and 77.8% on SWE-bench Pro represents a generational leap in AI-assisted coding. When Mythos-class capabilities eventually reach general availability (likely through a future Opus model with safety guardrails), expect complex debugging, multi-file refactoring, and end-to-end feature implementation to improve dramatically.
For cybersecurity professionals. Project Glasswing is your signal to engage. If you maintain critical software or open-source infrastructure, Anthropic is actively distributing credits and access. The 90-day reporting window means concrete findings and recommendations are coming soon.
For everyday AI users. You won’t get direct access to Mythos Preview, but its capabilities will trickle down. Anthropic has confirmed that Mythos-class safeguards will be tested on an upcoming Opus model, suggesting a more capable Claude is on the horizon. When that happens, Fello AI will give you access alongside every other frontier model (Claude, GPT, Gemini, DeepSeek, and more) in a single app across Mac, iPhone, and iPad.
AI models capable of finding decades-old vulnerabilities in the world’s most audited software represent both a serious risk and a powerful defensive tool. Project Glasswing is Anthropic’s bet that deploying these capabilities defensively, with the right partners and safeguards, is better than waiting for them to spread uncontrolled.
In related news, read how Claude Mythos was used to exploit Apple’s M5 chips.